Third Hand Plays: The Comedy of Encryption
Encryption is the age-old practice of taking a message, commonly known as a “plaintext,” and enciphering it to make it illegible to the unpracticed eye — this new text is known as the “ciphertext.” Prior to the use of ciphers, messages could be conveyed secretly by simply hiding them — shaving a messenger’s head, for example, and letting the hair grow back before sending him on his way, only to have it be revealed after a drastic haircut on the other end. Invisible ink was another common practice. A very basic form of encryption is known as the Caesar shift cipher, since Julius Caesar is the first to have used ciphers to exchange messages during war. This involved simply replacing a letter of the alphabet with, say, the letter five spaces to its right. A basic form of enciphered literary production is the Oulipian practice called N+7, in which a text, usually well known, has its nouns replaced by the nouns seven nouns down in a dictionary.
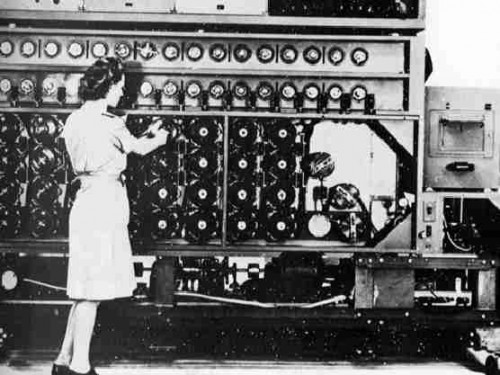
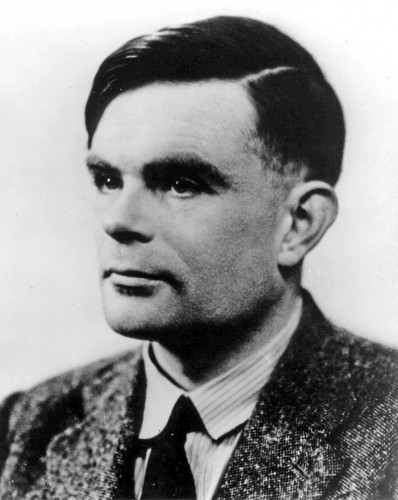
As Simon Singh describes in his wonderful The Code Book, encryption has found itself in the center of countless historical occurrences, from the beheading of Mary Queen of Scots — whose knowledge of the plot to kill Queen Elizabeth was revealed when one of her messages from prison was deciphered in court — to the failed attempt of Arthur Zimmerman, Germany’s foreign minister in World War II, to convince the Mexican president to attack the United States (and to, in turn, convince the Japanese emperor to do the same!) should the U.S. declare war once the Germans reinstated the practice of attacking ships with fully submerged U-boats (which increased the likelihood of sinking civilian vessels). One of the heroes of computer culture, Alan Turing, who conceived of the universal Turing machine — essentially the modern computer — is more generally known to the British public as the cracker of the Enigma code, developed by the Germans and involving a highly complicated machine that sent letters through several rotating disks that essentially changed the system of encipherment with each key stroke so that no patterns relating to normative language would be visible. But certain features of the Enigma cipher — such as its inability to encipher a letter as itself — allowed Turing’s machines, called “bombes,” to eventually deduce the system behind a large portion of the Germans’ messages, thereby averting several possible invasions and helping to plan D-day. (Turing, by the way, by most accounts a cheerful man, committed suicide after being forced to take hormones to “cure” him of his homosexuality.)
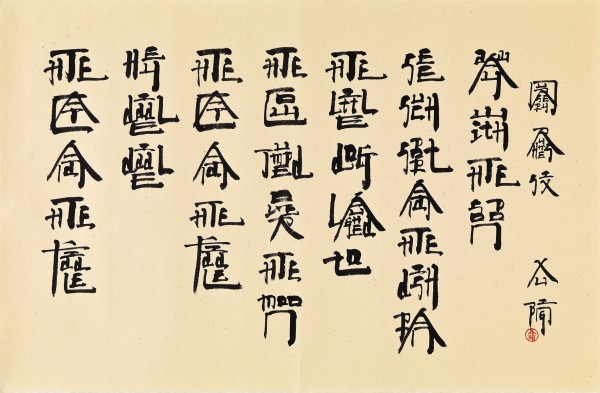
Elements of encryption can be seen in a few works we’ve looked at, such as Paul Chan’s “Alternumerics,” where the plaintext — say, the word Freud — is represented by a series of words, squiggles, or other types of iconography. Peter Cho’s interesting “Takeluma” project replaces letters with the visualization of their sound (culled from audio analysis software), which is, ironically, an attempt to make the sounds have an even more concrete relationship to the glyphs that represent them, rather than the arbitrary marks that we use today. Another artist who is, not perhaps coincidentally, Asian, is Xu Bing, who has crafted an entire system, called “New English Calligraphy,” for writing English language words using Chinese strokes. The reader of Chinese is thereby confronted with countless meaningless ideograms that nonetheless might have some Chinese radicals embedded in them — the box (to Western eyes) that represents the sun could be found in the word outside, but outside of that they are looking at gibberish. The eye of the English-language reader will initially see a classic Chinese ideogram, but on closer looking, she will discern words, and they will be almost entirely legible, even if the letters are arranged both vertically and horizontally, and in different sizes. It’s as if Ezra Pound’s claim in his writing on the Chinese ideogram (recently republished in a beautiful edition) as a unit of vocabulary came true: stare at an ideogram long enough and you will see the meaning.
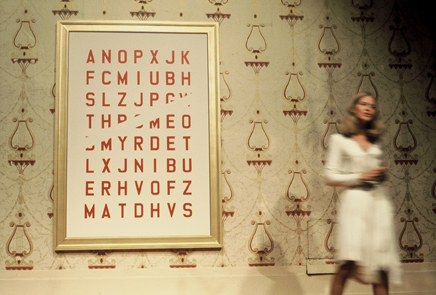
A relatively obscure Los Angeles artist named Guy de Cointet, who was born in France, made ciphers a central element of his texts and performances. His “drawings,” for example, usually included a piece of legible English text that framed what should have been the content of the piece, but which is often depicted as a mere jumble of letters. His self-published newspaper, ACRCIT, which MacLuhan praised, is a catalogue of encrypted texts — some in Morse code, Klingon (I think), etc. — with almost no legible text to ameliorate the experience. Reading it is like staring at a blank wall, but one that won’t let you rest easy with your thoughts. Cointet’s short plays (here is a YouTube clip) often hinged around the performers referring to the texts that were hanging on the wall — outside of some very ultra-modern, cubist furniture — and building narratives as if the messages they conveyed were frightfully transparent. Some of his works on paper can seem underwhelming at first, until you realize that, like with Alternumerics, embedded within them is some word, often the title itself, struggling to break through your ignorance and pass on … what? Cointet’s concerns for what we might call “content” were entirely overshadowed by his love of literary deadpan — getting you ready to have been stonewalled.
Works of electronic literature that play a part in this comedy include those works that involve algorithm to tweak the text without necessarily making it entirely illegible. For example, Talan Memmott’s “Self Portrait(s) [as Other(s)]” presents a number of classic biographies of early modernist heroes of painting, but they are chopped up, rearranged, and have noise introduced (in the form of anachronistic references to, say, Jeff Koons) such that we are provided with much relevant information, just not indexically attached to any known artist, living or dead. A plaintext hides behind this — there are, in fact, biographies where all of these details fit — but they become encrypted by the processes that mash them up into new wholes (a kind of programmatic detournement). The reader is put in the position of a game player, weighing this or that for its truth value, but also becomes increasingly aware of the very format of the hagiographic artist biography itself — its stages of early promise, initial discoveries, critical neglect, inevitable string of masterpieces, and ignominious, often early, death. Memmott’s first electronic literature productions were in “codework,” which is an invented creole mixing normative English text with elements from code (Alan Sondheim, coiner of the phrase, was another, and mez is probably the most well-known presently). Codework, too, can be seen as a form of “encrypted” text, as underneath the lively, noise-strewn surface is almost invariably something like a plaintext — the “message” — waiting to be consumed like a pot roast.
In fact, the comedy of encryption finds its greatest practitioner early on, in the figure of James Joyce. Though Finnegans Wake is often looked at as a terribly underdetermined text — where meanings are fluid, anything goes in terms of the underlying narrative content — in fact, upon further study (spending 15 weeks studying the first page, for example, which I did as a graduate student at CUNY), one finds that the text is terribly overdetermined, with meanings closed up and tidy once all of the multilingual allusions have been parsed. In the wake of Joyce have been a handful of writers who have “encrypted” their texts to a degree, most notably Anthony Burgess — who published his own Shorter Finnegans Wake and who for Clockwork Orange developed his own criminal argot, a mixture of Cockney and Russian slang with a few other things thrown in for good measure.
My favorite novel that employs an invented language, Riddley Walker by Russell Hoban, actually makes no real pretense to being representative of language thousands of years in the future; its puns, in the form of mystical crypto-scientific figures, are able to be decoded as much as understood. That is, the novel acts more as a puzzle pointing to some relatively static plaintext than some speculative, anthropological imagining of what language actually would look like millennia after the Apocalypse. Raymond Queneau’s Exercises in Style involves the rewriting of the same trivial short story with a hundred different methods (passive tense, extreme use of vulgarities, etc.) and puts the reader in the position of reading the encryption before the content. A final piece of literature, Kasey Mohammed’s ongoing Sonnagrams, for which he rewrites the sonnets of Shakespeare using only those letters that appear in the original poem, keeping them both legible, entertaining and, in the end, sonnets, could be seen as an example of the “comedy of recursion” I wrote about earlier. But in fact, they are part of the comedy of encryption, as they have a plaintext, but are written in a code that can’t be cracked without the help of those monkeys that, after an eternity, might just write the first five lines of Hamlet.